Stolen Data Can Now Disrupt & Contain An Attack.
Defensive AI Going Beyond Endpoint Protection
How AI is Changing the Cyber Landscape
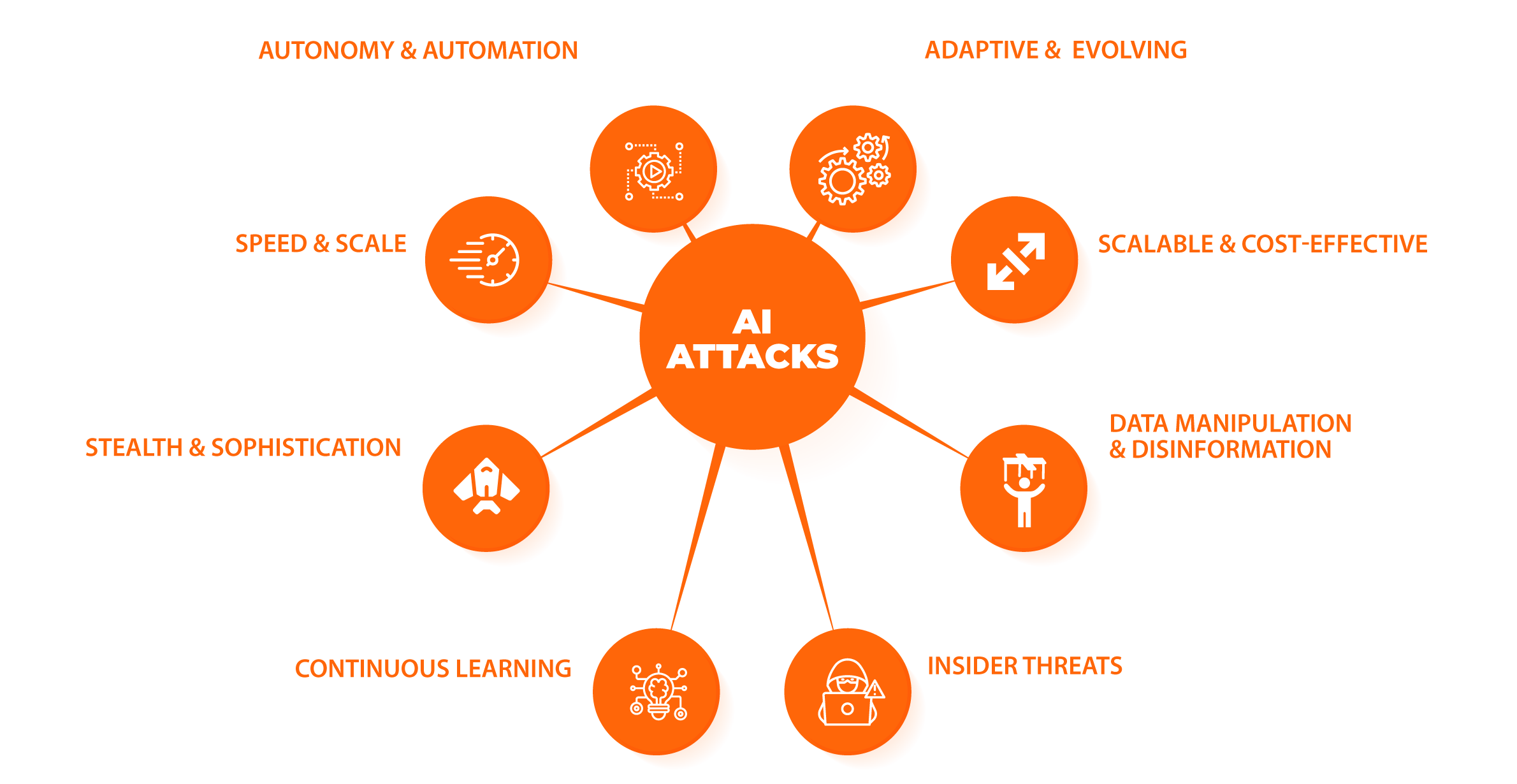
AI cyberattacks represent a new frontier in cybersecurity, leveraging automation and machine learning to carry out malicious activities. The evolved threat landscape has transformed from solitary hackers working in isolation to highly organized criminal enterprises that offer Cybercrime as a Service (CaaS). AI-driven attacks represent a groundbreaking revolution within the cybersecurity domain. Their autonomous, adaptable, swift, and scalable characteristics present a formidable challenge to both organizations and security experts.
Yesterday's Solutions Aren't Solving Today's Data Security Issues
Data Breaches in the Cloud
This year, 82% of breaches involve data stored in the cloud. While hybrid cloud environment breaches cost an averageof $3.8M, the average cost in private clouds was $4.24M and in public clouds it was $5.02M.
Explosive Data Growth
Most industry experts believe that 80% to 90% of the world’s data is unstructured, and according to IBM 90% of it has been created in the last two years alone. For larger organizations, it has already reached critical mass increasing the ever-growing attack surface.
Ransomware Payments Exceeded $1 Billion in 2023
In 2023, the ransomware landscape saw a major escalation in the frequency, scope, and volume of attacks marking a major comeback for ransomware. Record-breaking payments and a substantial increase in the scope and complexity of attacks—a significant reversal from the decline observed in 2022, which was forewarned by Chainalysis in their Mid-Year Crime Update.
Rise in Privacy Regulation
Data privacy regulations are becoming more widespread on a global scale. Stringent regulations such as the GDPR, PIPEDA, and CCPA are in full effect. Victims of data breaches now face mounting fines along with increased cyber insurance premiums which surged 79% in the US during 2022.
AI READY = CYBER READY
Transforming Cybersecurity for the AI Era
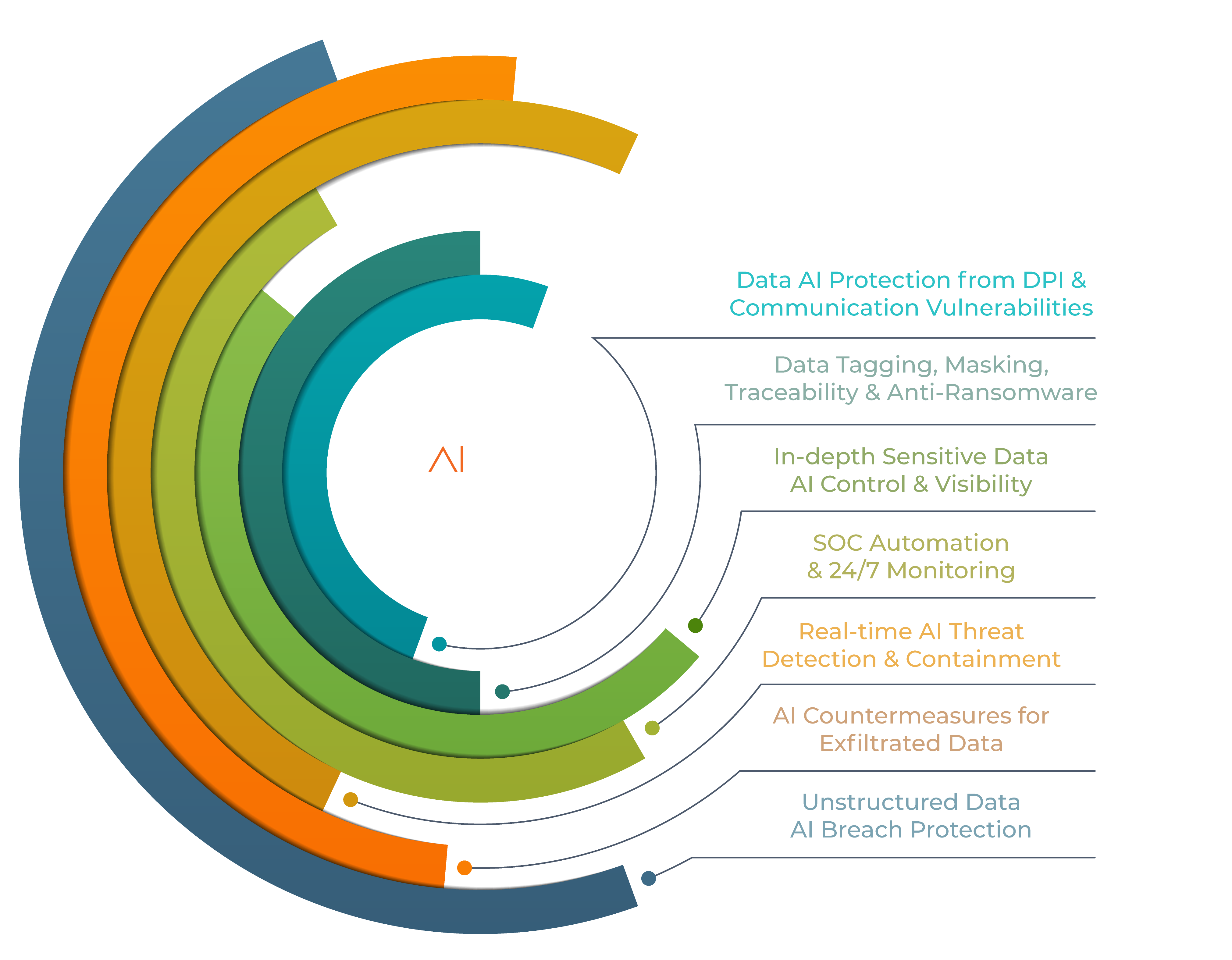
Automated AI is redefining protection for unstructured data by empowering the adversaries’ target—YOUR DATA—as the next line of defense. Data empowered with SCCAI™ enables your data to automatically sense and respond to its situation, all on its own.
The SCCAI FUSION™ security fabric brings defensive AI automation to MDR. Our proprietary, trusted SCCAI™ detects and contains data leakage attacks instantly to mitigate harmful data breaches. Gain sensitive data visibility and attack insights with this data-centric, rapid-response, lightweight AI. Advance your MDR operations with scalable, microsecurity that exists along with your current infrastructure.
See Our Features
Defensive, Automated AI Fabric for MDR
Leveraging our transformative AI Technology, we empower a new intelligent perimeter for TRUST, INTEGRITY, and PRIVACY.
SCCAI FUSION™ fabric enhances MDR capabilities with real-time, frictionless AI automation to scale and counter increasingly sophisticated threats.
- Increase efficiency and productivity: Automate time-consuming tasks, freeing up employees to focus on higher-level work.
- Overcome challenges by streamlining operations: Rapid automated AI response for MDR to detect and contain incidences in real-time.
- Enhance customer experiences: AI-powered assistance can provide 24/7 situational awareness of the customer’s sensitive unstructured data, improving customer satisfaction and retention.
- Realize competitive advantages: Implementing AI can give your business a competitive edge, allowing you to operate more efficiently and effectively than your competitors.
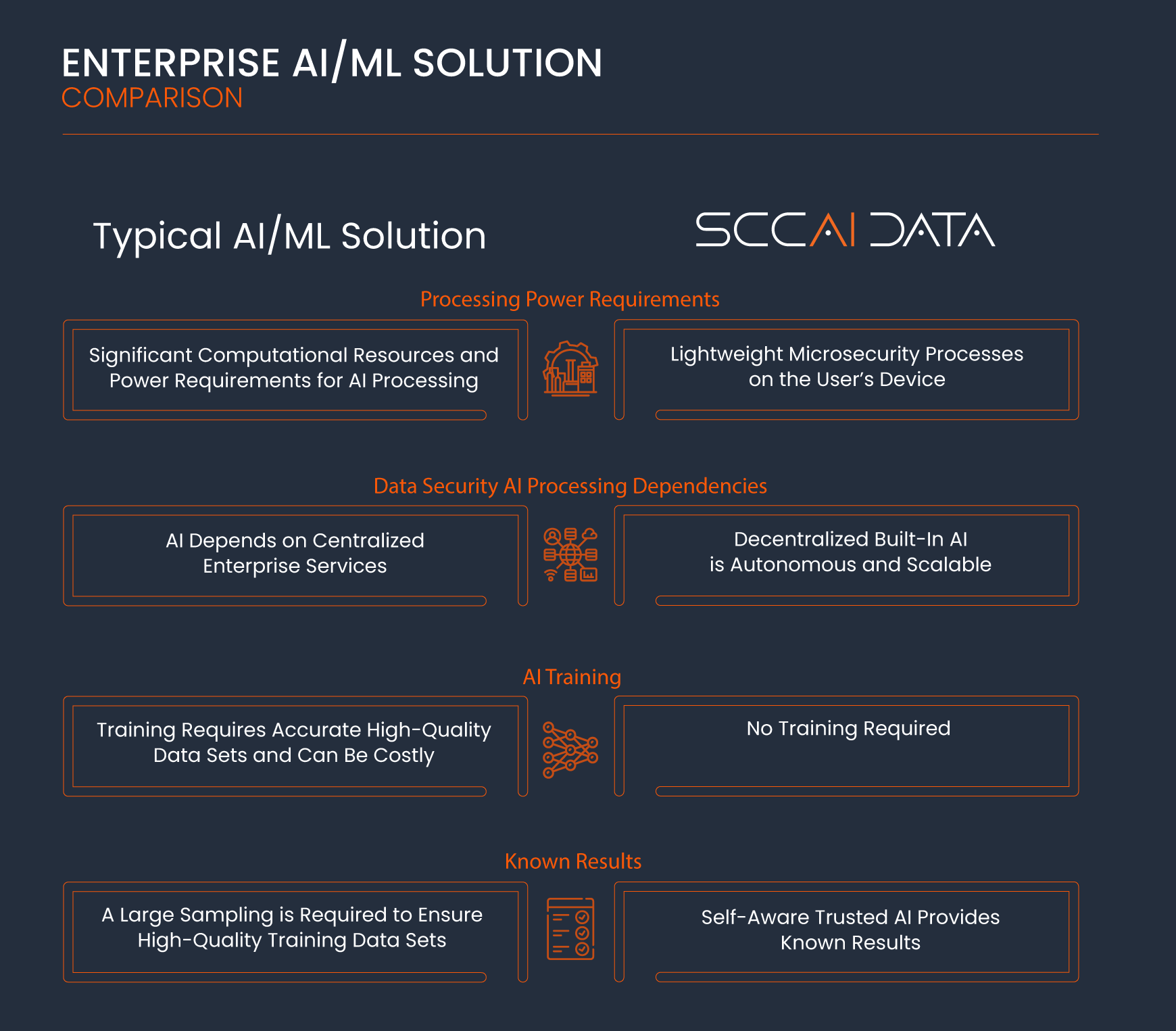
SCCAI FUSION™ fabric offers a unique approach when compared to other AI/ML Solutions available today!
Intufo has adopted a unique strategy in designing the SCCAI FUSION™ fabric. Our method sidesteps the substantial power and processing demands often associated with conventional AI/ML centralized solutions.
Through decentralized, lightweight SCCAI™ technology, we effectively process sensitive data while prioritizing defensive measures and employing Trusted AI™ for self-protection. This AI is compact enough to operate on users' devices without exceeding the processing consumption typically required for opening a standard data file.
Ease of Adoption
Simplicity of Use
Storage Agnostic
SCCAI VAULT™ can be located in on-premises, hybrid, and cloud storage locations.Protect Any Data Type
Any digital file type can be protected—typical, unique, and legacy systems data file formats.Co-exist with Current Solutions
SCCAI FUSION™ fabric co-exists with your current security stack.Zero Trust by Design
Upon activation, the SCCAI™ automatically verifies and validates its situation to control data access.Zero Knowledge (ZK) Encryption
Zero Knowledge is implemented to restrict sensitive unstructured data access to the organization only.Discover
Latest Features


AI EXPERTISE & INNOVATIONS
Intufo’s AI expertise includes innovations and patents in Electronic Warfare, SIGINT (Signal Intelligence), Adaptive Intelligent User Interface, Cognitive Technologies, Temporal Signal Intelligence, and Blockchain AI using neural networks, fuzzy inference and intelligent agents.
Contact UsAI
Areas of Expertise
Electronic Warfare
Best R&D Innovation Award
SIGINT Signal Intel
AI Classification System
Cognitive Technologies
Patented & Pen Tested
Intelligent Protocol
Patent Pending
Blockchain Microsecurity
Active Cyber Defense
Diagnostic Intelligence
Temporal AI Classification